DSA-2019: Debian Security Advisory: Lovestruck Leaders
Clients and friends have been asking a very similar question recently: what do the scandals in Debian and other free software organizations mean for me, my computers, my servers, my business?
Mustafa Aldawoodi publishes a white paper on social engineering.
I am quite sure most of you in the technology scene have heard of Social Engineering, right? Most kids use it for getting free things from companies; I must admit that I used to do this myself.
The evidence of Debian handing out thousands of dollars in diversity grants and receiving nothing in return sounds eerily similar. People may look at the photo of a former Debian leader surrounded by Albanian women and laugh at this scene yet when we look more closely, it is really scary: it is a recipe for every adversary who wants to infiltrate Debian and hasn't already done so. Simply send a group of smiling young women, sit back and watch as the developers fight and break rules.
Many people perceive social engineering as an attempt to gain access to confidential information, for example, successfully impersonating the queen to obtain medical records.
Yet social engineering attacks go much further. Sophisticated attackers encourage their targets to break rules in the hope that the shared knowledge of these crimes will give the attacker an opportunity to blackmail the target. Edward Snowden revealed an unsophisticated plot to entrap a Saudi banker in Geneva by orchestrating a drink driving violation.
Many of the attackers have a long-term view. They start by testing small rule violations and gradually lead their target deeper and deeper into the hot water.
Looking at the Debian diversity scandals, we find that just about every rule has been broken in a very short space of time:
- Age of consent: the Fedora Ambassador who recruited an underage girlfriend in Albania and was rewarded with a job at Canonical / Ubuntu
- People can't be paid to do work for Debian. This rule is written in the constitution where it states we are volunteers. Yet funds donated to Debian have been used to pay various women/girlfriends to do tasks when no volunteer was available. The first big indication of this was Nicolas Dandrimont's girlfriend applying for Outreachy.
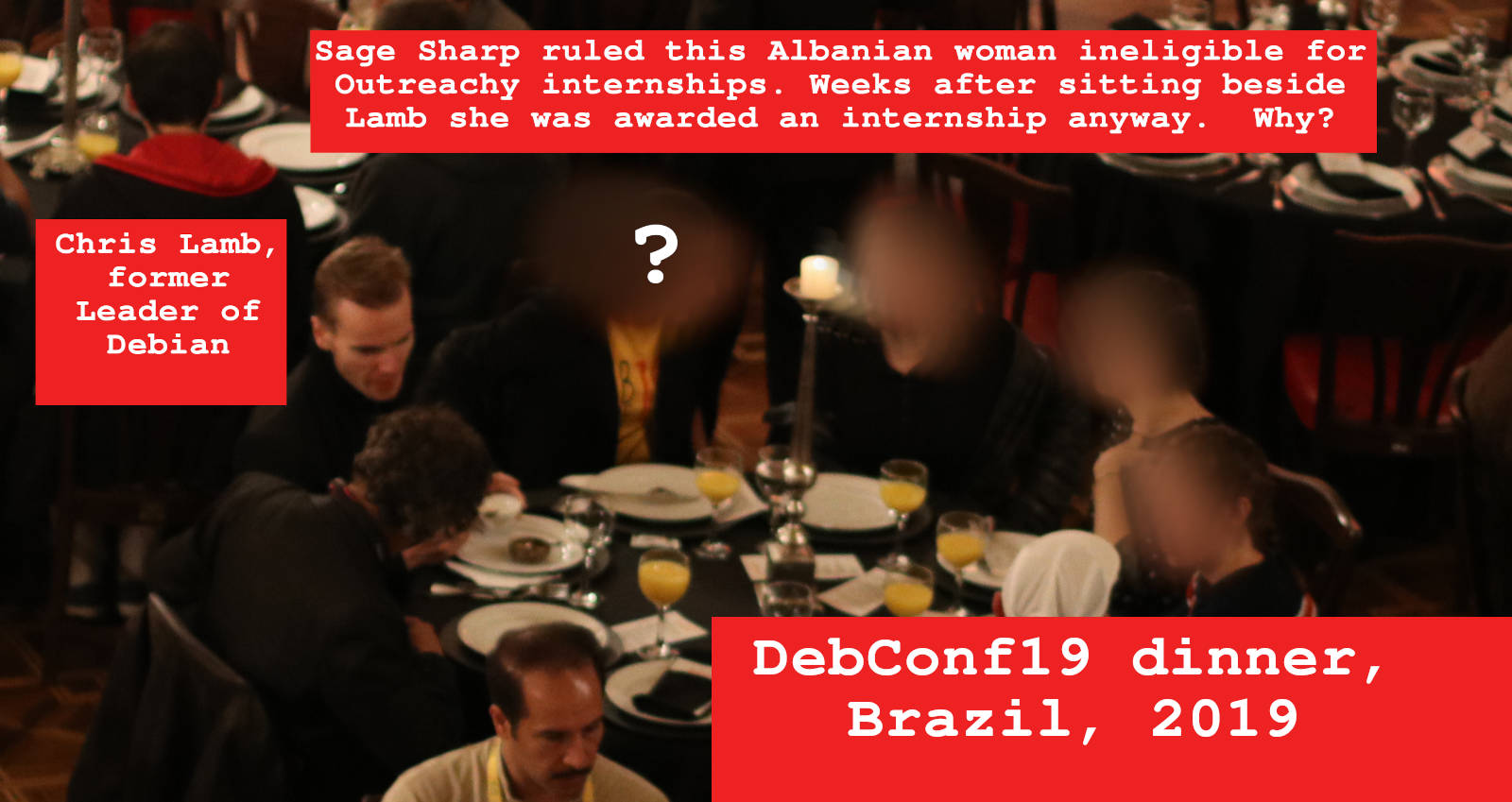
- DebConf must be organized completely by volunteers. Remember the refusal to pay for dishwashing services at DebConf13? This rule was broken shortly after DebConf19: the woman sitting next to the former leader at DebConf dinner was awarded an Outreachy internship to send emails promoting the next DebConf.
- People who have an existing history in free software activism can't be considered for Outreachy internships. Sage Sharp explicitly reminded us of this rule in 2017 when Debian first considered the woman in question. The rule was broken when Debian selected the woman anyway after she sat next to Lamb.
- Volunteers should not use gmail accounts to receive debian-private or any other sensitive emails. This rule is broken by many developers.
- Volunteers can not bring girlfriends or wives to DebConf. Yet it is obvious that some of the women awarded travel funds by the former leader did not come to DebConf on technical merit.
Once again, we need to come back to the question that started this blog: what does it mean for the user? These social engineering attacks under the guise of diversity may not compromise any of the archive keys or add new backdoors into the code. On the other hand, when ordinary volunteers see these rorts they may lose motivation. Fixes for security bugs, like everything else in Debian, depend on the motivation of volunteers to fix them promptly. A volunteer who was treated rudely at DebConf may simply leave a bug open for an extra week. High-impact projects that never finish: see the example of FreedomBox, which still hasn't made an official release after more than 12 years. Social engineering can play a role in all of these phenomena.
The overwhelming message here is that Debian has become a soft target for social engineering.
Please see some of my other pages about how Outreachy fell into disrepute.